Times are tough, the economy is in the tank, and if anything, times will get much tougher long before they get better.
Times are tough, the economy is in the tank, and if anything, times will get much tougher long before they get better.
We are all now faced with the task of trimming expenses this year, and software applications that cost hundreds of dollars are not going to be number one on our list of must haves.
Luckily, they don’t need to be.
There’s a wealth of tried and tested free software out in the wild blue of the Internet that will meet virtually every need you’re likely to have this year. Take a look at the following recommended free downloads that will help you communicate, get needed work done, have some fun, and manage and protect your system while you’re surfing the Internet.
To download the application/s of your choice, simply click on the application name.
Process those words:
OpenOffice:
OpenOffice 2 is the leading open-source office software suite for word processing, spreadsheets, presentations, graphics, databases and more. It is available in many languages and works on all common computers. It stores all your data in an international open standard format and can also read and write files from other common office software packages including Microsoft Word.
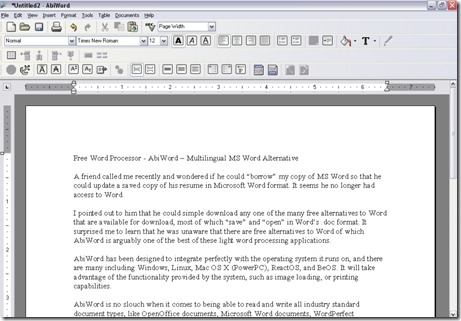
AbiWord:
AbiWord is a free light weight word processing program similar to Microsoft Word. It is suitable for a wide variety of word processing tasks.
WordWeb:
WordWeb is a one-click English thesaurus and dictionary for Windows that can look up words in almost any program. It works off-line, but can also look up words in web references such as the Wikipedia encyclopedia.
Manipulate and correct your pics – put them online:
FastStone Image Viewer:
This is one of my favorite photo applications, with good reason. It’s not just a viewer, but an image browser, converter, and an editor as well. You’ll find the interface intuitive and very easy to use. This program is loaded with features including, renaming, cropping, color adjustments, lossless JPEG transformation, drop shadow effects, image frames, scanner support, histogram and much more.
IrfanView:
IrfanView is a very fast, small, compact and innovative graphic viewer for Windows 9x/ME/NT/2000/XP/2003/Vista. Strange name – terrific application.
Google Picasa:
A free software that helps you locate and organize all the photos on your computer, edit and add effects to your photos with a few simple clicks and share your photos with others through email, prints and on the web.
Play those tunes:
Audacity:
Audacity is free, open source software for recording and editing sounds. It is available for Mac OS X, Microsoft Windows, GNU/Linux, and other operating systems. Definitely the best of breed.
iTunes:
According to Apple this is the world’s best digital music jukebox. Download music, TV shows, movies, and more.
Winamp:
A multimedia player that supports numerous audio and video formats. It also plays streamed video and audio content, live and recorded, authored worldwide.
Watch your fav videos:
Miro:
Miro is a free application for channels of internet video (also known as ‘video podcasts and video rss). Miro is designed to be easy to use and to give you an elegant full screen viewing experience.
VLC:
A highly portable multimedia player for various audio and video formats (MPEG-1, MPEG-2, MPEG-4, DivX, mp3, ogg …) as well as DVDs, VCDs, and various streaming protocols.
Free FLV Converter:
This free software let you search YouTube and dailyMotion videos without opening your browser and you can even watch the videos using the built-in video player.
Free Video To iPhone Converter:
Convert video files to Apple iPhone MP4 video format. Convert the whole movie or select a partition from the movie to convert (trim video).
iPod Video Converter:
Free iPod Video Converter provides an easy and completed way to convert all popular video formats to iPod video.
Better browsing:
FireFox:
FireFox includes tons of useful features such as tabbed browsing, built-in and customizable search bars, a built-in RSS reader and a huge library of extensions developed by thousand of developers.
Opera:
Opera introduces Speed Dial which vastly improves navigation to your favorite sites. In addition, there’s Fraud protection, anti-phishing detection keeps browsing safe and secure.
Web of Trust (WOT):
WOT is a free Internet Browser add-on (my personal favorite), that has established an impressive 4.5/5.0 star user rating on CNET. WOT tests web sites you are visiting for spyware, spam, viruses, browser exploits, unreliable online shops, phishing, and online scams, helping you avoid unsafe web sites.
Protect your system:
Spyware Doctor Starter Edition:
This free version of the award winning program, with its easy to use interface, is used by millions of people worldwide to protect their computers; it’s reported there are a million+ additional downloads every week.
AVG Anti-Virus:
AVG Anti-Virus Free now incorporates protection against spyware through a new combined anti-virus and anti-spyware engine as well as a “safe-searching component” which has been incorporated into the new AVG Internet Security Toolbar. This program scans files on access, on demand, and on schedule and scans email incoming and outgoing. For those on Vista, you’re in luck, it’s Vista-ready
Comodo Firewall Pro:
The definitive free firewall, Comodo Firewall protects your system by defeating hackers and restricting unauthorized programs from accessing the Internet. I have been using this application for 10 months and I continue to feel very secure. It resists being forcibly terminated and it works as well, or better, than any firewall I’ve paid for. This is one I highly recommend. Amazing that it’s free!
Staying in touch:
Windows Live messenger:
The next generation MSN Messenger. It comes with everything that were already available in Messenger, and a new i’m Initiative that makes helping your favorite charity as easy as sending an instant message.
Pidgin:
A multi-protocol Instant Messaging client that allows you to use all of your IM accounts at once. Pidgin can work with: AIM, Bonjour, Gadu-Gadu, Google Talk, ICQ, IRC, MSN, Yahoo!, MySpaceIM and many more.
Trillian:
A fully featured, stand-alone, skinnable chat client that supports AIM, ICQ, MSN, Yahoo Messenger, and IRC.
System Tools:
CCleaner:
CCleaner is a freeware system optimization, privacy and cleaning tool. It removes unused files from your system – allowing Windows to run faster and freeing up valuable hard disk space. It also cleans traces of your online activities such as your Internet history. Additionally it contains a fully featured registry cleaner. But the best part is that it’s fast; normally taking less than a second to run.
Glary Utilities:
Glary Utilities, a free all-in-one utility, is a terrific collection of system tools and utilities to fix, speed up, maintain and protect your PC. Personal experience with this application for the last 8 months has convinced me that a typical user can really benefit by having this application on their system. With this free program you can tweak, repair, optimize and improve your system’s performance; and its ease of operation makes it ideal for less experienced users.
Revo Uninstaller:
Revo Uninstaller is a superior program to uninstall programs from your computer. This free program with its advanced and fast algorithm scans before, and after you uninstall an application. After the program’s regular uninstaller runs, you can remove additional unnecessary files, folders and registry keys that are usually left over (those “orphaned” registry entries we talked about earlier), on your computer. This feature is a definite plus.
 There’s a lot of tech jargon when reporting the new variant of the Conficker worm, Conficker B++. We’ll skip it.
There’s a lot of tech jargon when reporting the new variant of the Conficker worm, Conficker B++. We’ll skip it.