World Backup Day: Do you backup your files? UK will finally allow citizens to legally rip CDs; Refresh your PC for spring with these top apps; Malwarebytes 2.0 Still Tough on Malware; Three essential tools for solving the worst Wi-Fi headaches; Beginner’s guide to Google Now voice-activated personal assistant; Ubuntu 14.04 is slickest Linux desktop ever; Why Linux Mint is a worthwhile Windows XP replacement; Watch out for photos containing malware; The problem with cloud security cameras; Microsoft will no longer look through your Hotmail to investigate leaks.
World Backup Day: Do you backup your files? – How protected is your digital life? If your house burned to the ground, would you still have your important photos, documents, financial information and more? Or would you be back at square one?
UK will finally allow citizens to legally rip CDs – An update to UK copyright law means that from June 1, 2014 it will no longer be illegal to make copies of CDs—or e-books or any other media—that you have bought for personal use. It will remain, however, illegal to make copies at home for friends and family. (So no passing on those ripped CDs, people!) If you want to give the CD to a loved one, you should make sure you delete any personal copies you have made from it, explains the Intellectual Property Office (IPO).
10 cool Bluetooth devices for your iPhone or Android – It’s an odd thought: peripherals for your smartphone, which itself is often considered a peripheral to your computer. But as mobile devices become computing devices in their own right, a cornucopia of peripherals is emerging.
Three essential tools for solving the worst Wi-Fi headaches – Thanks to improvements to routers and network management software, connecting to Wi-Fi is vastly easier than it used to be. But that doesn’t mean the experience is seamless quite yet. Even now you can still run into problems like poor signal quality, dropped connections, lack of public hotspots, and slow speeds. Sick of the hiccups? These three programs can help take the headache out of Wi-Fi woes.
Beginner’s guide to Google Now voice-activated personal assistant – Learn how to configure and use Google Now, Android’s voice-driven personal assistant and Google’s answer to Apple’s Siri. With the release of Android 4.4 and phones like the Moto X and Nexus, Google Now has become a seriously useful tool. In this TechRepublic Two Minute Drill, Jack Wallen shows you how to set up Google Now and demonstrates a few ways it can help make your Android experience hands-free.
How Dropbox Knows When You’re Sharing Copyrighted Stuff (Without Actually Looking At Your Stuff) – The system is neither new, nor sketchy. It’s been in place for years, and it’s about as unsketchy as an anti-copyright infringement system can get. It allows Dropbox to block pre-selected files from being shared from person-to-person (thus keeping Dropbox from getting raided by the Feds), without their anti-infringement system having any idea what most of your files actually are.
Refresh your PC for spring with these top apps – Every machine needs tune-ups, and that includes your PC. Without regular cleaning and updates, your system performance suffers, slowed down by hefty files and unneeded software. Fortunately, many fine — and free! — utilities can do the system spring cleaning for you. Here’s a roundup of our favorites.
Six clicks: Weird tricks that will actually make you happier with Windows 8.1 – Each new update chips away at the annoyances of Windows 8. Here are six power features that are new or improved with the Windows 8.1 update due in a couple of weeks.
Microsoft’s freemium Office apps jump to top of iPad chart – Microsoft’s new Office for iPad apps vaulted to the top of the free application chart on Apple’s App Store shortly after their Thursday debut. The long-awaited, highly anticipated apps — Word, Excel and PowerPoint — were ranked No. 1, 2 and 3 early today on the App Store’s free iPad app list. OneNote, which had already been in the App Store — it was also refreshed yesterday — held down the No. 4 spot, giving Microsoft four of the top five for the iPad.
Malwarebytes 2.0 Still Tough on Malware, Now with a Pretty Face – After ten years of version 1.x, Malwarebytes has finally released version 2.0. The powerful malware-fighting tools are all still there, but the package is a lot better looking. A new dashboard page displays security status; if anything isn’t right, you just click Fix Now. And you can track progress of updates and scans right in the dashboard. Rootkit detection, once a separate component, is now integrated. A variety of other once-awkward mechanisms have been streamlined for ease of use. It’s quite an improvement. Want to know more? Read my full review. Malwarebytes remains our Editors’ Choice for free, cleanup-only antivirus.
Ubuntu 14.04 is slickest Linux desktop ever – Ubuntu LTS releases understandably tend toward the conservative end of the spectrum when it comes to new features. You’re not going to see Unity 8 in this release, nor will there be any trace of the Mir graphics stack that Canonical is hoping will – one day – support both its desktop and mobile offerings. Rather, this release sees a bunch of small, incremental improvements to Unity and the addition of some long-missing features Canonical had previously rejected. It’s the latter that makes Trusty Tahr the most surprising, particularly since, in both cases, Ubuntu developers explicitly rejected the ideas when they were initially proposed.
16 weirdest places you’ll find Linux – Linux is everywhere, from desktops and servers to phones and televisions. Let’s take a look at some of the stranger places you’ll find Linux installed.
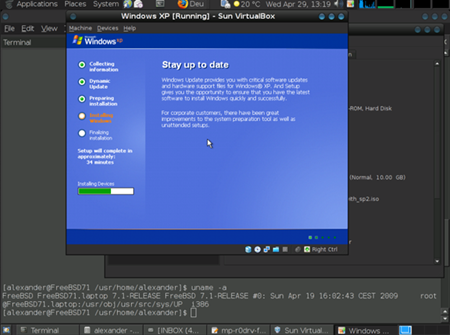
Why Linux Mint is a worthwhile Windows XP replacement – XP’s support life is quickly coming to an end. Fortunately for Windows XP users, there’s a Linux desktop–Linux Mint–that has the same look and feel but with far better security and speed.
hereO is a trendy GPS watch for kids – Mobile technology and mobile devices are so prevalent today that it totally make sense to employ those not just to make our lives easier but keep our families safer as well. hereO offers just that, injecting GPS technology into a watch that, at the same time, looks cool enough that kids will want to keep them on.
WD brings out new Thunderbolted external drive – WD has bought out a Thunderbolted My Passport Pro external drive with power delivered over the speedy data cable. It comes in 2TB and 4TB capacities using two 2.5-inch drives, with either RAID 0 (striping) or RAID 1 (mirroring) for MAC users. RAID 0 delivers up to 233MB/sec bandwidth with the 2TB unit but 230MB/sec with the 4TB unit, using the integrated Thunderbolt cable. WD says that’s roughly twice as fast as USB 3.0 with RAID 0 set, when transferring a 22GB high-definition video file.
Demonoid returns after nearly two years, popular Bittorrent tracker is back online – Community based BitTorrent tracker and website, Demonoid, has made a comeback after being down for nearly two years due to various copyright infringement complaints from governments around the world.
Proposed mandatory age checks for porn sites for UK visitors – Increased crackdowns are being proposed by UK industry (Video-on-Demand) watchdogs Atvod in a bid to reduce the access rate of pornograhpy by children (minors under 18 years of age by UK law).
3 app building services for building an Android business app – You have a business and you want to expand that business into the realm of mobility. Unfortunately, you don’t have the finances to hire a programmer to create an Android app that would take your niche shop out into the world. Thankfully, there are sites available that allow you to build that app without having to write a single line of code. Unfortunately, these services have yet to reach a sort of ‘drag and drop Nirvana’ where you can piece together a full-fledged, powerhouse app; but for anyone wanting to get their business known via mobile apps, this is the way to go.
Security:
How Fandango and Credit Karma exposed millions of smartphone users’ data – Developers of two popular smartphone apps—Fandango and Credit Karma—have been caught transmitting passwords, social security numbers, birth dates, and other highly sensitive user data over the Internet without properly encrypting it first, officials with the Federal Trade Commission said. As a result, it was trivial for hackers to intercept the data when people used the apps on both Apple’s iOS and Google’s Android mobile operating systems, complaints filed by the FTC alleged. The complaints leveled charges of other shortcomings in the developers’ security, including the failure to properly test and audit the safety of apps before making them available for download. The improper encryption, which security experts warn is akin to having no encryption at all, was allowed to persist for four years at Fandango. The company also failed to have an adequate process for receiving vulnerability reports from researchers and other third parties, FTC officials said.
Watch out for photos containing malware – Cybercriminals use images in a number of ways to infect your computer. In most cases, the photo itself is harmless; it’s just a trick to get you to do something stupid. But sometimes, a .jpg file itself will contain malicious code. Let’s look at a few ways in which an image can contain some real bad news.
Journalists increasingly under fire from hackers, Google researchers show – According to a new paper authored by two Google security engineers, 21 out of the world’s top 25 news organizations have been successfully hacked by state-sponsored actors. Among targets of hacking attacks, journalists were “massively over-represented,” Shane Huntley, one of the paper’s authors, told the news wire. Google has been monitoring such attacks, which are often sponsored by foreign governments that seek sensitive information held by journalistic enterprises, in many cases related to secretive corporate and governmental operations.
Microsoft will no longer look through your Hotmail to investigate leaks – Amid widespread privacy concerns in the wake of a leak investigation, Microsoft has announced a change in the way it handles private customer accounts. Under the new policy, effective immediately, any investigation that suggests that Microsoft’s services have been used to traffic stolen Microsoft intellectual property will no longer result in Microsoft accessing private account information. Instead, the investigation will be handed over to law enforcement agencies, and it will be for those agencies to demand access to necessary private information.
The problem with cloud security cameras – Wi-Fi security cameras are great for giving you piece of mind or checking on the kids and babysitter while you’re out. But after working with several models for about six months I’ve come to realize that in some situations they’re no substitute for a professionally managed home security system.
Banks pulls out of class-action suit against Target, Trustwave – One of the two banks suing Target and security vendor Trustwave over responsibility for one the largest data breaches in history has pulled out of the lawsuit. Trustmark National Bank, of New York, filed a notice of dismissal of its claims on Friday in U.S. District Court for the Northern District of Illinois. It had joined Green Bank of Houston in the class-action suit, which claims Target and Trustwave failed to stop the theft of 40 million payment card details and 70 million other personal records.
Company News:
Google Cracks Down On Deceptive Ads And Other Shady Behaviors Found In Android Apps – Android apps are about to get cleaned up. That is, if the recently added changes to the Google Play Developer Program Policy are actually enforced. Google this week updated its policy that dictates to app developers what sort of content their apps are permitted to display, with a number of rules designed to crack down on shady and deceptive ads.
Last.fm to end their subscription music service on April 28 – The company stated that they had to make “some very difficult decisions surrounding [their] core products and services” which led them to shut down their subscription music service.
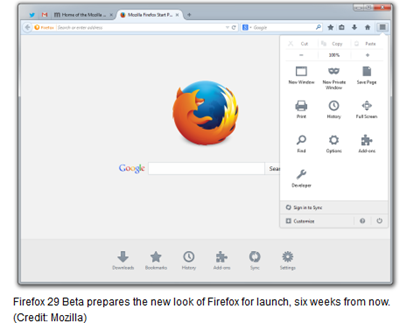
Half of Mozilla’s board resign over the choice of Brendan Eich as Mozilla CEO – Three members of Mozilla’s six-member board have reportedly stepped down over the choice of Brendan Eich as the new CEO. The three Mozilla board members to resign are former Mozilla CEO and current head of AVG Gary Kovacs, another former CEO named John Lilly, and Ellen Siminoff, CEO of the online education startup Shmoop. The reason for their departure appears to be focused around their demands for someone from outside Mozilla with a background in the mobile industry, presumably to help push Firefox OS and to seize a larger share of the mobile browser market.
BlackBerry reveals when to expect BBM for Windows Phone – BlackBerry’s CEO, John Chen, has given a clearer timeframe on when the company will launch its BBM app for Windows Phone, adding that some Lumia and Nokia X handsets will come with BBM pre-installed.
Games and Entertainment:
Two years later, Reaper of Souls is the Diablo III we always wanted – The battle for the soul of Diablo III is over. “What kind of game is this?” was a question asked from its very start, thanks to the seemingly over-the-top, always-online infrastructure that marred the game’s launch. This was exacerbated by the institution of in-game Auction Houses trading in both in-game gold and real money, a system loved by gold sellers but loathed by pretty much everyone else. Then there was the overly self-serious storyline, an odd fit for a game intended to be played and replayed at higher and higher difficulties. Now, after two years of play and patching, Diablo III has finally realized what it wants to be—and it’s much better for it.
Origin goes all-digital: EA’s store ditching disks – Come April 4th and all of the games at EA’s Origin game store will be available as digital downloads only. What this means is that the store has phased out discs, hence shoppers will no longer be able to buy a physical collection. The digital downloads will be available for PC and Macs.
Study: Most Millennials Don’t Watch TV on the TV – For younger millennials aged 14 to 24, the bulk of entertainment time is spent on laptops, smartphones, tablets and Internet-connected video gaming systems — with only 44 percent of them watching TV on a television, according to a new study.
Star Wars VII may trigger new Indiana Jones trilogy without Harrison Ford – It’s strange how things work out sometimes. For anyone who was old enough to watch Indiana Jones and the Raiders of the Lost Ark when it first released back in 1981, there is only one Indy, and that’s Harrison Ford. He’s since done three more movies in the series, and a fifth has been talked about ever since the Kingdom of the Crystal Skull hit theaters. The problem is, Ford is now 71 years old. Although still capable of handling a whip and a gun, Harrison Ford may not be Indiana Jones in the next movie. But it isn’t his age that would stop him. No, it’s an even bigger movie franchise called Star Wars.
Off Topic (Sort of):
J. Edgar Hoover would have loved the internet – The case of Edward Snowden and the subsequent revelations about the behaviors of the NSA raise serious questions about privacy, liberty and the future role of the internet, by way of J. Edgar Hoover.
Facebook ‘I drank’ post not best idea for woman on DUI probation – The day after St. Patrick’s Day, a young woman has to take a random breathalyzer test. She passes. She goes on Facebook to say she’d actually been drinking. Guess what happens next.
The Improbable Rise Of Roku – In 10 years, when we look back and think about which companies fundamentally changed the way viewers get their TV shows delivered to them, will Roku be a part of the conversation? Based on what the company has done to date, and where it’s going, it seems likely.
The Internet Is Held Together With Bubble Gum And Baling Wire – Did you know that, to quote an angry hacker: The Internet from every angle has always been a house of cards held together with defective duct tape. It’s a miracle that anything works at all. Those who understand a lot of the technology involved generally hate it, but at the same time are astounded that for end users, things seem to usually work rather well.
Architects in Amsterdam to construct full-scale 3D printed homes – The convenience of 3D printing has moved away from industrial design and products to architecture. We are not talking about scale models to showcase the blueprints or interiors, but in fact full-scale homes. The 3D Print Canal House designed by Dus Architects is as close to a concept structure as it is to art, and will soon dot the landscape of Amsterdam.
Physics explained in 10 mind-bending GIFs – Just because the laws of physics are consistent, that certainly doesn’t mean they always make sense to our squishy mammal brains. Our day to day experiences don’t include advanced materials, superconducting magnets, or extreme temperatures. You might be sure your eyes are deceiving you when dealing with something like that, but it’s just science. We’re going to use GIFs to zero in on just that kind of thing — weird physics that makes you scratch your head. Don’t worry, we’ll explain it all too.
Something to think about:
“Be kind – Remember every one you meet is fighting a battle – everybody’s lonesome.”
– Marion Parker
Today’s Free Downloads:
Gom Player – A multimedia player which can play most of the differently encoded video formats that include AVI, DAT, MPEG, DivX, XviD, and more with its own built-in codec system. GOM Player supports most of the condecs (AVI, DAT, MPEG, DivX, and plus more) by its own embedded codec system that you won’t have to look for appropriate codecs everytime when you can’t play a certain video format. GOM is also able to play incomplete or damaged AVI file by skipping the damaged frames. And it can also playback Locked Media Files while downloading or sharing (with real-time index rebuilding under certain condition: AVI downloading in consecutive order). GOM also supports HTTP Streaming ASF/OGG/MP3/AAC/MPEG PS/MPEG TS: Only work with internal splitters). GOM also support its own skins, Subtitle, Overlay Mixer features, Optimized buffer for streaming Automatic ASF source filter, Keys Remapping, Superspeed/High Mode, Enhanced Filter Rendering and full-Unicode.
MediaHuman YouTube to MP3 Converter – You like to listen to music on YouTube or Vimeo and want to save it for offline playing. Or you want to download soundtrack of a new movie. Then MediaHuman YouTube to MP3 Converter is the best choice for you. Better than online converters. Downloads highest available quality. YouTube, Vimeo, Soundcloud, Dailymotion, VEVO. Simultaneous downloads. Simple tag editor. Allows saving in original quality. Playlist support. Importing to iTunes. (Awesome application!)
In Pursuit of Freedom – The Pushback Continues:
Der Spiegel: NSA Put Merkel on List of 122 Targeted Leaders – Secret documents newly disclosed by the German news magazine Der Spiegel on Saturday shed more light on how aggressively the National Security Agency and its British counterpart have targeted Germany for surveillance. A series of classified files from the archive provided to reporters by NSA whistleblower Edward Snowden, also seen by The Intercept, reveal that the NSA appears to have included Merkel in a surveillance database alongside more than 100 others foreign leaders. The documents also confirm for the first time that, in March 2013, the NSA obtained a top-secret court order against Germany as part of U.S. government efforts to monitor communications related to the country. Meanwhile, the British spy agency Government Communications Headquarters targeted three German companies in a clandestine operation that involved infiltrating the companies’ computer servers and eavesdropping on the communications of their staff. Der Spiegel, which has already sketched out over several stories the vast extent of American and British targeting of German people and institutions, broke the news last October that Merkel’s cellphone calls were being tapped by the NSA – sparking a diplomatic backlash that strained US-Germany relations. Now a new document, dated 2009, indicates that Merkel was targeted in a broader NSA surveillance effort. She appears to have been placed in the NSA’s so-called “Target Knowledge Base“ (TKB), which Der Spiegel described as the central agency database of individual targets. An internal NSA description states that employees can use it to analyze “complete profiles“ of targeted people.
NSA’s UK partner targets German companies, says report – A new report based on the trove of NSA documents leaked to journalists last year by Edward Snowden says the agency’s UK counterpart, the GCHQ, spied on German Internet firms, and it provides more information on the NSA’s efforts to monitor German Chancellor Angela Merkel. The report, published in German magazine Der Spiegel, quotes one of the documents as saying that Britain’s Government Communications Headquarters sought “development of in-depth knowledge of key satellite IP service providers in Germany,” with an eye toward, as the publication puts it, “developing wider knowledge of Internet traffic flowing through Germany.” The GCHQ was not only interested in surveilling Net traffic, it also wanted to, Der Spiegel reports, “identify important customers of the German teleport providers, their technology suppliers as well as future technical trends in their business sector,” and the intelligence outfit also targeted company employees, especially engineers, for monitoring.
US Takes a Break From Condemning Tyranny to Celebrate Obama’s Visit to Saudi Arabia – Today, Obama arrives in Riyadh to assure the Saudi monarchs that the US is as committed as ever to its close partnership in the wake of Saudi anxiety. He’ll meet with King Abdullah, “the president’s third official meeting with the king in six years.” The purpose of this trip: “trying to smooth relations with Saudi Arabia without making the longtime US ally seem like an afterthought.” Indeed, “top presidential advisors say the visit is an ‘investment’ in one of the most important US relationships in the Middle East.” If you want to justify all of this by cynically arguing that it benefits the US to support repressive and brutal tyrannies, go ahead. At least that’s an honest posture. But don’t run around acting as though the US is some sort of stalwart opponent of political repression and human rights violations when the exact opposite is so plainly true. And if you’re someone who has worked extensively to provide the world’s worst regimes with all sorts of vital support, don’t hold yourself out as the leader of the mob condemning others for expressing support for far more benign governments.
US to strengthen privacy rights for Euro bods’ personal data transfers: Makes commitment under ‘Safe Harbour’ framework – The US will take steps before the summer to comprehensively strengthen the “Safe Harbour” framework that helps facilitate some transfers of personal data to the US from the EU. The commitment to improve privacy protections (10-page/445KB PDF) was contained in a joint statement issued on behalf of senior officials from the EU and US, including president of the European Council Herman Van Rompuy, president of the European Commission Jose Manuel Barroso and US president Barack Obama. It follows a threat from the European Parliament to veto any future trade agreement between the EU and US unless safeguards for EU citizens’ privacy rights were improved by the US.
China’s CERT blames US for a THIRD of all attacks on Middle Kingdom PCs: Government sites declared a ‘disaster area’ – China’s Computer Emergency Response Team (CNCERT) has claimed in a new report that backdoor attacks on systems jumped by over 50 per cent over the past year, and once again fingered the US as the main culprit in 2013. It claimed that 15,000 “hosts” taken over by “APT Trojan”, while 61,000 sites were hit by backdoor attacks launched from overseas in 2013, a rise of 62 per cent. In total, 10.9 million Chinese PCs were infected and controlled from outside the Great Firewall last year with the US accounting for 30.2 per cent of attacks. South Korea and Hong Kong were also named as common attack sources. Akamai’s most recent State of the Internet report, for example, claims the top two countries by attack source are China (35 per cent) and Indonesia (20 per cent), with the US some way behind in third with 11 per cent. That said, if the Snowden leaks can be believed, the US is doing itself no favours in the battle against China for the moral high ground.
Huawei on NSA: If foreign spies attacked a US firm, there’d be “outrage” – It’s been a week since revelations that the National Security Agency infiltrated the systems of Huawei, and the Chinese technology company is still trying to determine the extent of the attacks and whether they are still going on. In an interview with Ars yesterday, Huawei VP of external affairs Bill Plummer said, “We’re very early in the process of determining what has happened… The goal is ‘let’s find out what, if anything, happened, and let’s make sure it’s not still happening, and let’s take the appropriate measures to make sure it can’t happen in the future.” What is certain is that Huawei argues that the US government’s actions are unacceptable.