The waiting game is almost over for Harry Potter fans who are hungry to feast their eyes on the much-anticipated final chapter in the Harry Potter franchise – Harry Potter and the Deathly Hallows Part 2.
The waiting game is almost over for Harry Potter fans who are hungry to feast their eyes on the much-anticipated final chapter in the Harry Potter franchise – Harry Potter and the Deathly Hallows Part 2.
There are always those of course who won’t wait – in this case until July 15. You know the type – the buttinskis who push ahead of you in line, or cut you off on the expressway – the ones you’d like to clunk upside the head.
Unfortunately, the obnoxious dimwits who behave in this way, tend to repeat this behavior across a broad range of personal activity, and I suspect, that the niceties of copyright law is well below their personal radar horizon.
The reigning experts in social engineering – cybercriminals (who, in my view, could teach “legitimate social engineering experts” a thing or two), are well aware of the “can’t wait buttinskis”, and in a perfect replay of the old “there’s no honor amongst thieves”, have made available through free torrent downloads –Harry Potter and the Deathly Hallows Part 2, except…
Except – PC Tools, the company which brings you PC Tools Firewall Plus (free), ThreatFire (free), and of course a complete line of award-winning commercial grade security offerings, has discovered that these free torrent downloads are nothing more than a new online malicious scam. Gotta admit – I love Karma payback!
I’m posting the bulletin PC Tools sent me yesterday on this, since it’s very instructive in terms of just how much effort cybercriminals will go through, in order to penetrate a target’s computer.
It’s not often possible to capture an online attack as it occurs, but in this case, PC Tools managed to do just that – see images and links listed below.
Here’s how the malicious scam works:
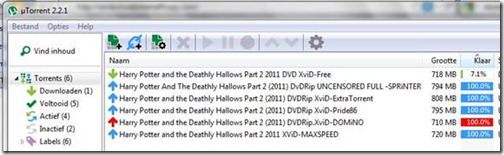
- First, a user searches torrents for free downloads of the final Harry Potter movie
- Results claiming to offer a free download of the new movie appear
- Once users download the file, .RAR file and password.txt downloads appear
- Users receive a message saying, “This video is password protected to stop automated leeching and detection. To get your password, please visit:
- Here, users are taken through a series of instructions to obtain their password.
One of which is choosing a link for a special offer while the site “verifies” the password
- Once users click on an offer, a new tab and pop-up open, asking users to save what seems to be a legitimate file
- After saving the file, cybercriminals have access to your computer—and the movie, of course, never appears on the screen
Harry Potter Threat Exposed
Here’s what victims find while searching for the Harry Potter and the Deathly Hallows Part 2 movie or videos:

Users can discover apparently ripped versions of the new Harry Potter movie on file-sharing websites.
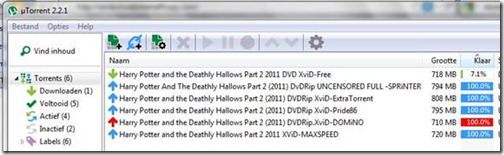
It looks like the movie is being downloaded on the victim’s computer.

The victim is instructed to decompress the archive.

RAR and password.txt files suddenly appear.

User is told to visit separate website by password.txt file.

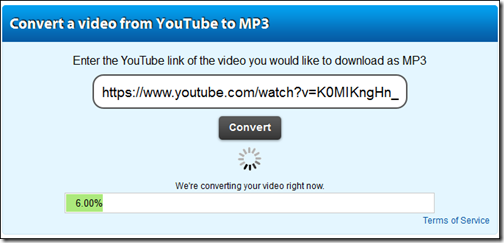
The victim then sees this screenshot, claiming to be MovieYT.com.

User follows 3-step instructions, which takes them to a verification code check.

User clicks on VLC Player and a new tab is opened.

When hovering over the download button, the download executable file looks real.

Once the user clicks on the file, they are prompted to save it – this, of course, contains malware.

While all this is happening, the user is still waiting for the “Verification Check” from MovieYT – but the cybercriminals now have access to the victim’s computer. They have your password and other personal information that they can use to further attack you, your finances, your friends and social networks.
Worth repeating: Consider the trade-offs, and the very real risks involved with Peer to Peer and Torrent applications.
Privacy: When you are connected to file-sharing programs, you may unintentionally allow others to copy confidential files you did not intend to share. So be sure to setup the file-sharing software very carefully.
If you don’t check the proper settings when you install the software, you could allow access not just to the files you intend to share, but also to other information on your hard drive, such as your tax returns, email messages, medical records, photos, and other personal and financial documents.
It’s extremely important to be aware of the files that you place in, or download to, your shared folder. Don’t put information in your shared folder that you don’t want to share with others. Your shared folder is the folder that is shared automatically with others on peer to peer file sharing networks.
Copyright Issues: You may knowingly, or otherwise, download material that is protected by copyright laws and find yourself caught up in legal issues. Copyright infringement can result in significant monetary damages, fines, and even criminal penalties.
Some statistics suggest as many as 70% of young people between the ages of 9 – 14, regularly download copyrighted digital music. If you are a parent, you bear the ultimate responsibility for this illegal activity.
Adult Content: Again, if you are a parent you may not be aware that their children have downloaded file-sharing software on the family computer, and that they may have exchanged games, videos, music, pornography, or other material that may be unsuitable for them. It’s not unusual for other peoples’ files to be mislabeled and you or your children can unintentionally download these files.
Spyware: There’s a good chance that the file-sharing program you’re using has installed other software known as spyware to your computer’s operating system. Spyware monitors a user’s browsing habits and then sends that data to third parties. Frequently the user gets ads based on the information that the spyware has collected and forwarded to these third parties.
I can assure you that spyware can be difficult to detect and remove. Before you use any file-sharing program, you should buy, or download free software, that can help prevent the downloading or installation of spyware, or help to detect it on your hard drive if it has been installed.
Viruses: Use and update your anti-virus software regularly. Files you download could be mislabeled, hiding a virus or other unwanted content. Use anti-virus software to protect your computer from viruses you might pick up from other users through the file-sharing program.
Generally, your virus filter should prevent your computer from receiving possibly destructive files. While downloading, you should avoid files with extensions such as .exe, .scr, .lnk, .bat, .vbs, .dll, .bin, and .cmd.
Default Closing Behavior: It is critical that you close your connection after you have finished using the software. In some instances, closing the file-sharing program window does not actually close your connection to the network. That allows file-sharing to continue and will increase your security risk. Be sure to turn off this feature in the programs “preferences” setting.
What’s more, some file-sharing programs automatically run every time you turn on your computer. As a preventive measure, you should adjust the file-sharing program’s controls to prevent the file-sharing program from automatically starting.
If you found this article useful, why not subscribe to this Blog via RSS, or email? It’s easy; just click on this link and you’ll never miss another Tech Thoughts article.
 St. Patrick’s Day is over for another year – and, thank goodness for that. Along with New Years Eve, St. Paddy’s Day, it seems to me, brings out the worst in the non-drinking drinkers who load-up well past their capacity to handle the juice of the barley. As an Irishman (of some renown
St. Patrick’s Day is over for another year – and, thank goodness for that. Along with New Years Eve, St. Paddy’s Day, it seems to me, brings out the worst in the non-drinking drinkers who load-up well past their capacity to handle the juice of the barley. As an Irishman (of some renown ![]() ), I do celebrate St. Patrick’s Day – but, in comfort – at home – with good friends – and, a boatload of Guinness.
), I do celebrate St. Patrick’s Day – but, in comfort – at home – with good friends – and, a boatload of Guinness.